OpenCVE Now Supports KEV and EPSS Metrics
We’re thrilled to announce that OpenCVE now supports two powerful new threat metrics: KEV and EPSS.
These additions help teams go beyond CVSS scores and focus on the vulnerabilities that truly matter.
What Are KEV and EPSS?
KEV (Known Exploited Vulnerabilities) is a catalog maintained by CISA listing vulnerabilities that are known to be actively exploited in the wild. If a CVE is on this list, it’s a high-priority risk.
EPSS (Exploit Prediction Scoring System), developed by FIRST.org, assigns a probability (0–100%) that a vulnerability will be exploited within the next 30 days, based on real-world data.
Unlike CVSS, which evaluates theoretical severity, KEV and EPSS provide real-world exploitation context.
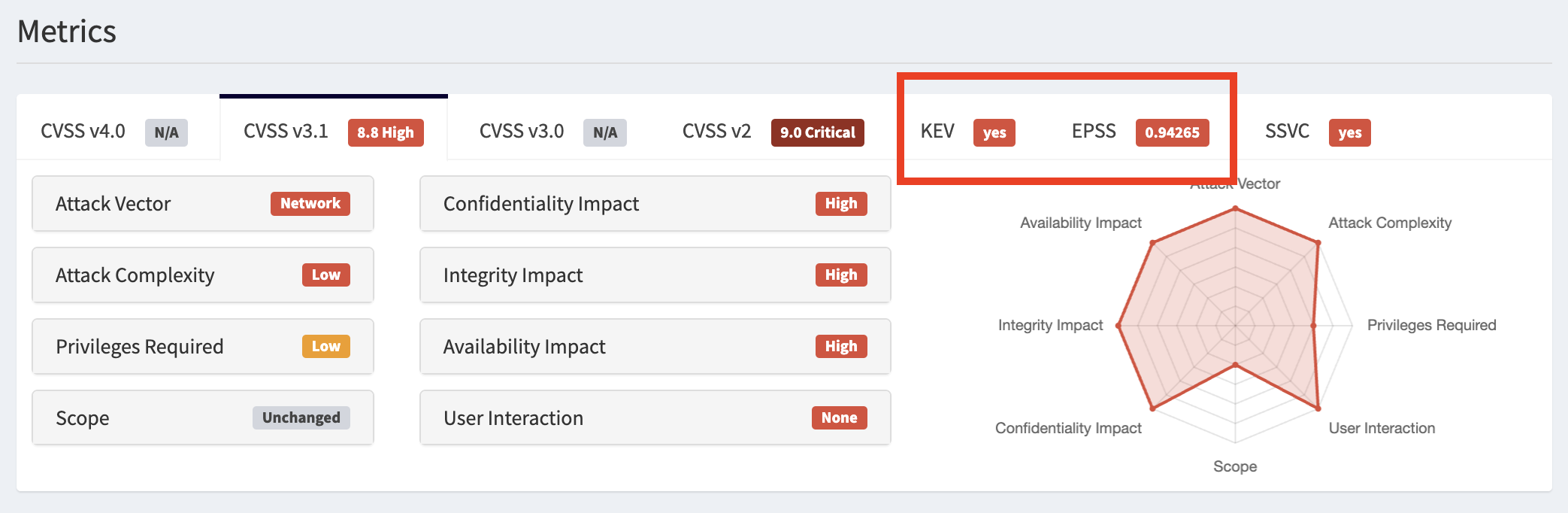
Why does it matter? Let’s take CVE-2021-34527 (PrintNightmare) as an example:
- CVSS Score: 8.8
- KEV: Present in the catalog
- EPSS: 94.26%
This tells you it’s not just a critical vulnerability, it’s being exploited and has a high chance of recurring exploitation.
New KEV and EPSS Query Filters
OpenCVE now lets you search vulnerabilities using these new filters:
kev:true: Only CVEs listed in the CISA KEV catalogepss>=80: Only CVEs with a high EPSS probability (80% or more)epss>='0.75': You can also use decimal values
You can combine them with existing filters like CVSS, vendor, product, and tags. For example: vendor:microsoft AND kev:true AND epss>=80 AND cvss31>=8.
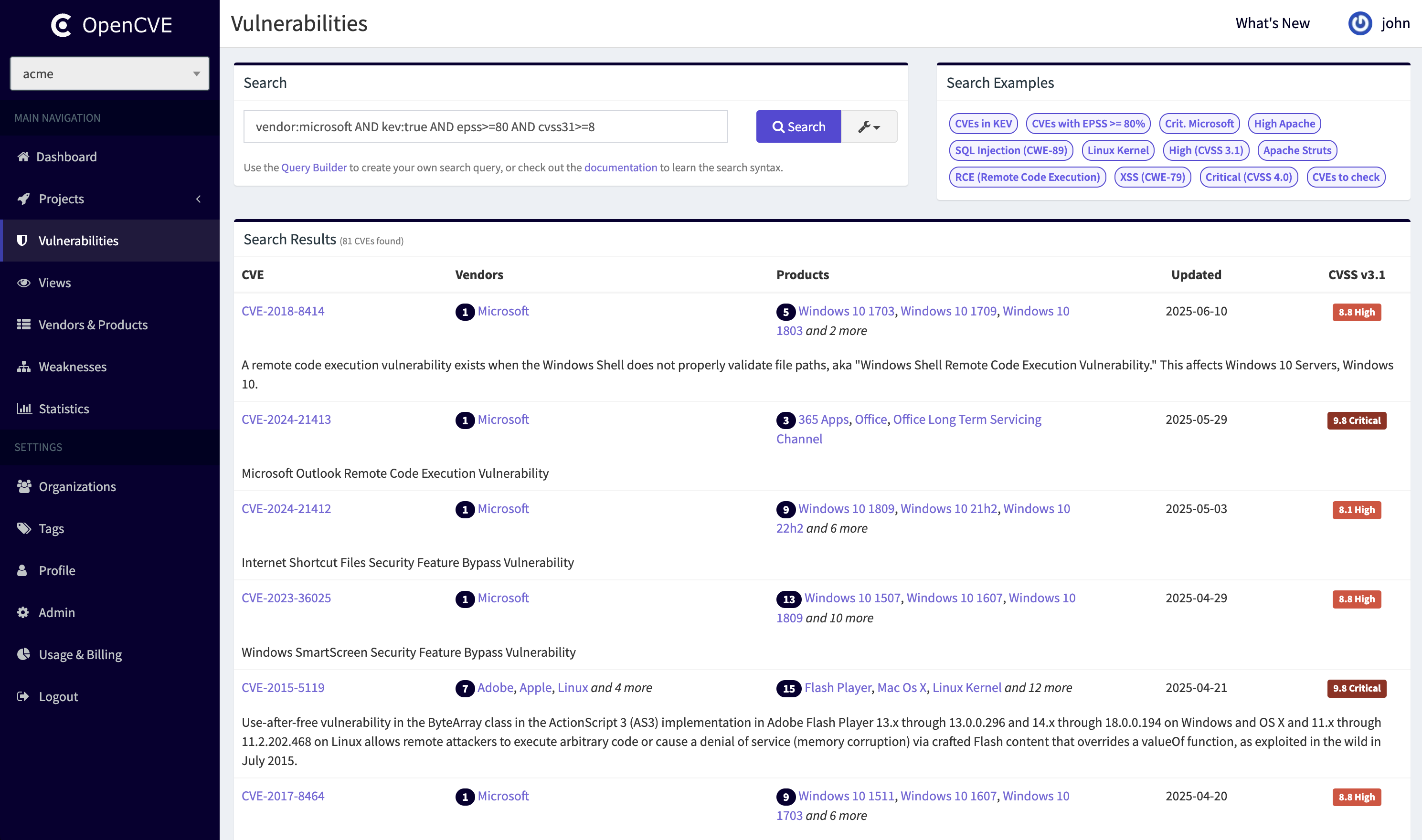
This query shows only critical, exploitable Microsoft CVEs, giving you a much clearer view of what needs urgent attention.
Focus on What Matters
With KEV and EPSS support, OpenCVE becomes even more actionable:
- ✅ Prioritize threats being exploited in the wild
- ✅ Predict what’s likely to be attacked next
- ✅ Reduce noise, focus your triage
👉 Try it now on the CVE page: https://app.opencve.io/cve.