OpenCVE Enrichment: AI-Powered CVE Analysis
A few months ago, we introduced OpenCVE Enrichment, our AI-powered system to automatically extract vendors and products from CVEs that lack official metadata. Today, we’re taking it several steps further: introducing CVE analysis, turning raw vulnerability data into actionable insights.
Why This Matters
To appreciate what’s new, it’s worth revisiting the problem we set out to solve.
OpenCVE has always relied on CPE data from the NVD to associate CVEs with vendors and products. When a user subscribes to mozilla:firefox, they receive alerts for every CVE linked to that product. Simple and effective. Until the NVD started falling behind.
Since early 2024, the NVD has significantly reduced its CVE enrichment activity. As a result, a large portion of newly published CVEs arrive with no CPEs, no CVSS score, and no structured product data. In January 2025 alone, only 29% of published CVEs had at least one CPE. That means the vast majority of vulnerabilities land in a blind spot: no vendor, no product, no user alert.
On top of that, even when CNAs do provide vendor and product names, the formatting is inconsistent. The same vendor might appear as Foo Bar, foobar, or Foo Bar Software across different CVEs. Without normalization, these would never be recognized as the same entity.
What OpenCVE Enrichment Already Does
To address this, we built a pipeline that runs on every incoming CVE:
- An internal LLM analyzes the CVE’s title, description, and references to extract candidate vendor/product pairs with confidence scores.
- A fuzzy matching layer reconciles those suggestions against OpenCVE’s internal knowledge base, handling typos, abbreviations, and naming inconsistencies.
- Validated results are integrated into the platform.
This ensures that even CVEs with minimal metadata are correctly linked to their affected vendors and products. Your subscriptions keep working, regardless of NVD delays.
That alone is a significant guarantee for any security team that relies on OpenCVE to stay on top of vulnerabilities. But we didn’t stop there.
What’s New
We’ve expanded OpenCVE Enrichment with several additions that make the data even richer and more actionable.
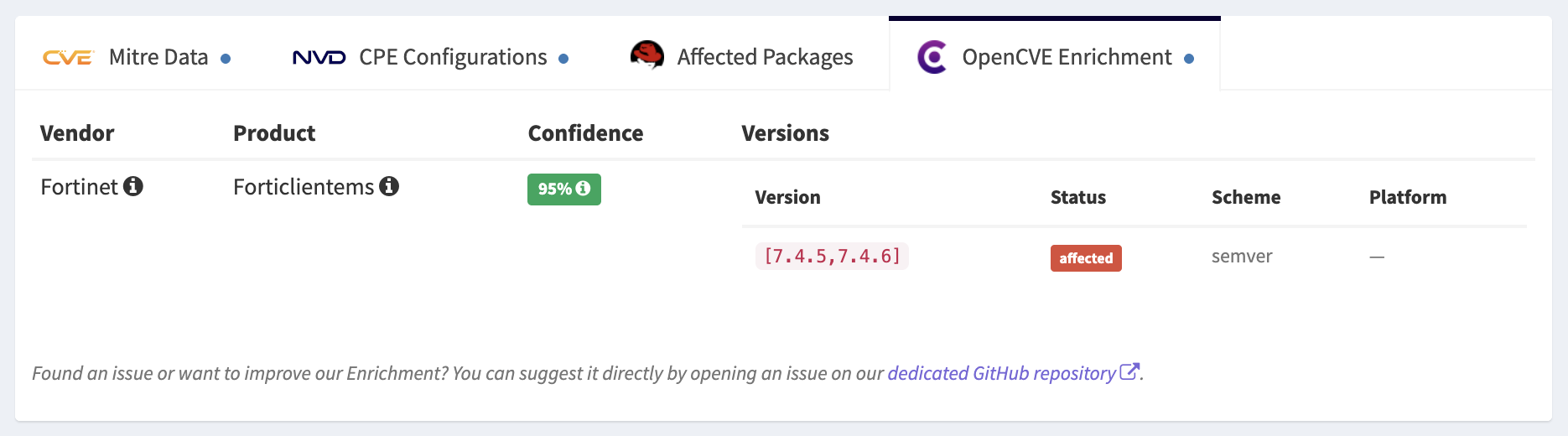
Version detection. Beyond identifying vendors and products, Enrichment now extracts structured version information from CVE data: which versions are affected, which are patched, and under what conditions. This lays the groundwork for precise version-level filtering when searching for impacted components.
CWE assignment. When a CVE has no associated weakness category, OpenCVE Enrichment now infers and assigns a CWE based on the vulnerability description. This improves classification accuracy and helps with filtering and prioritization.
Title generation. Some CVEs are published with a missing or generic title. Enrichment can now generate a clear, descriptive title when none is present, making it easier to understand a CVE at a glance without reading the full description.
AI-Powered CVE Analysis
This is the headline feature of this release.
CVE descriptions are often terse, written for technical reviewers and not for the people who actually need to act on them. A description like “sandbox escape due to incorrect boundary conditions in the WebRTC networking component” is factually accurate, but leaves a lot of questions unanswered: What can an attacker actually do? Which systems are exposed? What should I do right now?
In practice, this means security teams have to read and interpret raw CVE descriptions manually, often under time pressure.
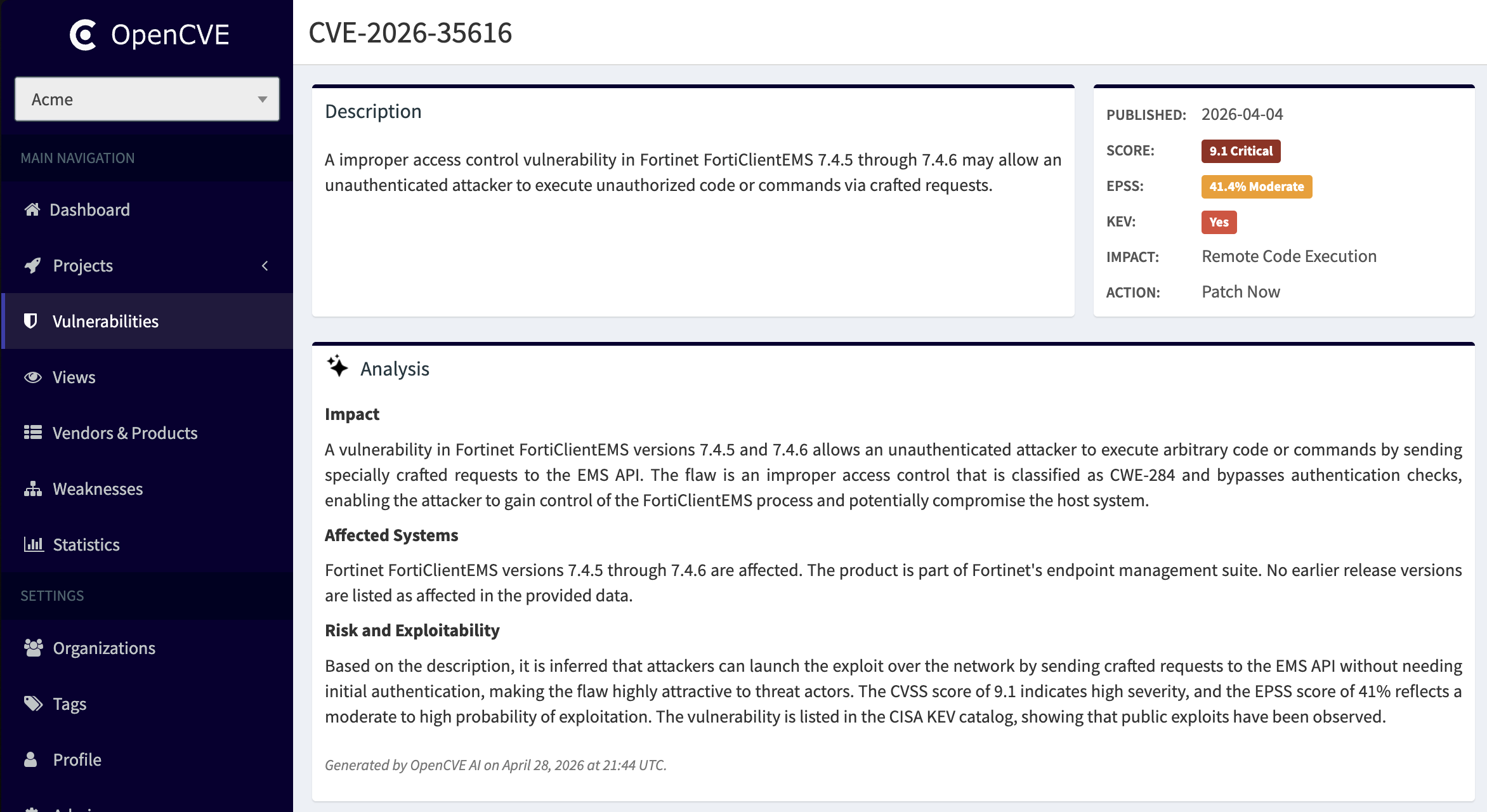
OpenCVE Enrichment now automatically analyzes every incoming CVE using a trained AI model and produces a structured report with four sections:
- Impact: what the vulnerability allows an attacker to do, and what the consequences could be.
- Affected Systems: which products, versions, and configurations are at risk.
- Risk and Exploitability: an assessment of severity, CVSS context, EPSS availability, and known exploitation status.
- Recommended Actions: concrete steps to remediate or mitigate the issue.
A Real Example
Let’s look at CVE-2026-7321, a critical vulnerability affecting Firefox and Thunderbird. Here is the raw description as published by Mozilla:
Sandbox escape due to incorrect boundary conditions in the WebRTC: Networking component. This vulnerability was fixed in Firefox 150, Thunderbird 150, and Firefox ESR 140.10.1.
Short, factual, and not particularly actionable. What does a “sandbox escape” actually mean in practice? What’s the blast radius?
Here’s what OpenCVE Enrichment produced:
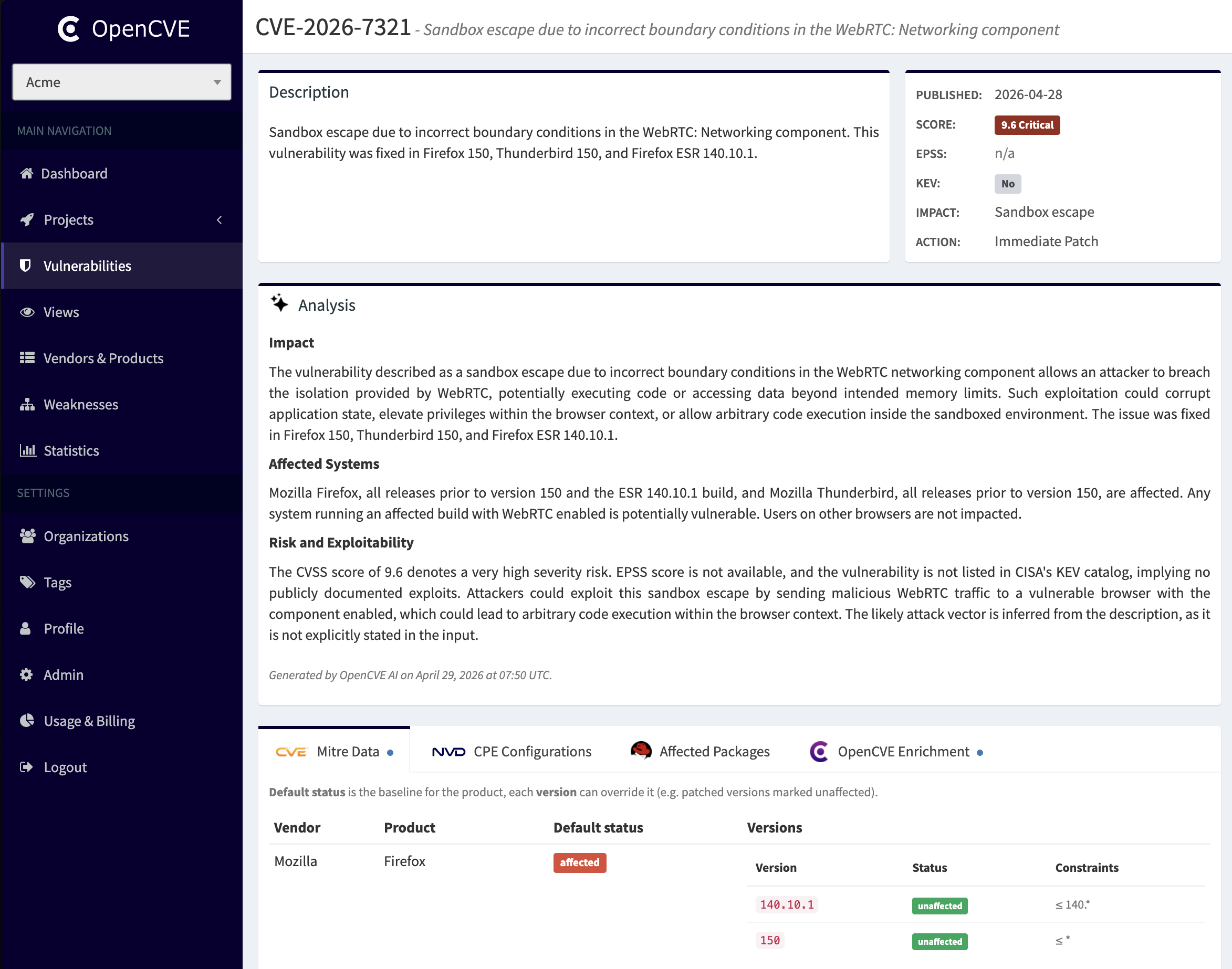
Impact
The vulnerability described as a sandbox escape due to incorrect boundary conditions in the WebRTC networking component allows an attacker to breach the isolation provided by WebRTC, potentially executing code or accessing data beyond intended memory limits. Such exploitation could corrupt application state, elevate privileges within the browser context, or allow arbitrary code execution inside the sandboxed environment.
Affected Systems
Mozilla Firefox, all releases prior to version 150 and the ESR 140.10.1 build, and Mozilla Thunderbird, all releases prior to version 150, are affected. Any system running an affected build with WebRTC enabled is potentially vulnerable. Users on other browsers are not impacted.
Risk and Exploitability
The CVSS score of 9.6 denotes a very high severity risk. EPSS score is not available, and the vulnerability is not listed in CISA’s KEV catalog, implying no publicly documented exploits. Attackers could exploit this sandbox escape by sending malicious WebRTC traffic to a vulnerable browser with the component enabled, which could lead to arbitrary code execution within the browser context.
Now compare that to the original description. The analysis surfaces what’s actually at stake: privilege escalation, arbitrary code execution, network-reachable attack vector. Things that matter when deciding how urgently to act.
👉 This is the difference between reading a CVE and understanding it instantly.
Actionable Remediation
Mozilla’s advisory mentions the fixed versions, but nothing more. OpenCVE goes further. When no explicit remediation is provided, our AI generates recommended actions tailored to the vulnerability:
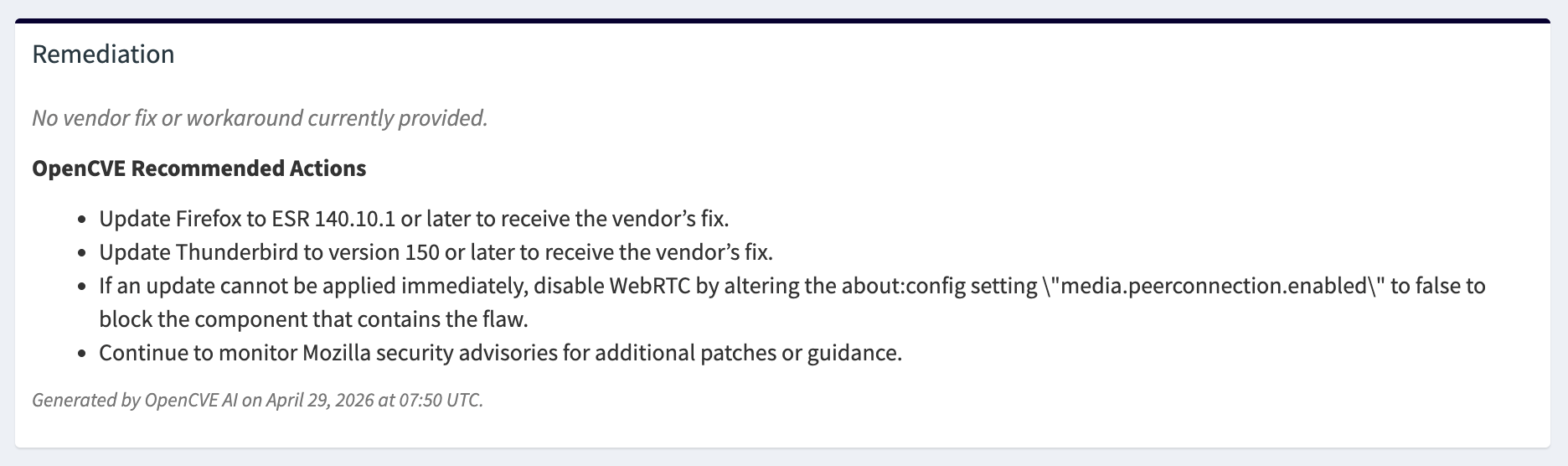
- Update Firefox to ESR 140.10.1 or later to receive the vendor’s fix.
- Update Thunderbird to version 150 or later to receive the vendor’s fix.
- If an update cannot be applied immediately, disable WebRTC by altering the
about:configsettingmedia.peerconnection.enabledtofalseto block the component that contains the flaw.- Continue to monitor Mozilla security advisories for additional patches or guidance.
That third point is particularly valuable. In real-world environments, applying a patch immediately isn’t always possible. Having a documented workaround that actually mitigates the vulnerable component can make the difference between exposure and protection while the update is being rolled out.
Available on OpenCVE Cloud
AI-powered CVE analysis is available exclusively on OpenCVE Cloud.
Vulnerability management is a daily challenge, and the volume of CVEs keeps growing. Our goal with OpenCVE is to help security teams cut through the noise: not by drowning them in raw data, but by surfacing what’s relevant, what’s urgent, and what to do about it.
We hope these improvements make your CVE monitoring meaningfully more efficient.
👉 Start using OpenCVE Cloud and turn CVEs into actionable insights in seconds.